The Quiet Rise of a Massive Browser-Based Attack
The discovery of over one hundred malicious Chrome extensions marks a turning point in how attackers are exploiting the modern web. What makes this campaign particularly dangerous is not just its size, but its subtlety. These extensions were not obvious threats. They were designed to blend into the Chrome Web Store ecosystem, appearing as legitimate tools while quietly building a distributed network of compromised browsers.
Instead of relying on a single developer identity, the attackers deliberately fragmented their presence across multiple publisher accounts. Names like Yana Project, GameGen, SideGames, Rodeo Games, and InterAlt gave the illusion of unrelated creators operating independently. In reality, they were all part of the same coordinated operation. This approach allowed the campaign to scale without triggering immediate suspicion, ultimately reaching roughly twenty thousand installations before being flagged.
From a security standpoint, this is a textbook example of how trust in platform ecosystems can be exploited. Users tend to assume that anything available in an official store has been vetted. Attackers understand this assumption and are increasingly designing campaigns that weaponize that trust.
A New Level of Access: Why Browser Extensions Are So Dangerous
Browser extensions operate in a uniquely powerful position within the software stack. Unlike traditional applications, they sit directly inside the user’s browsing environment, where nearly all sensitive activity takes place. Emails, financial transactions, cloud dashboards, messaging platforms—everything flows through the browser.
Because of this, extensions often request broad permissions. Many users approve these requests without hesitation, granting access to read and modify data across all websites. In the wrong hands, that level of access is equivalent to handing over the keys to your entire digital life.
What makes this campaign particularly concerning is how effectively it leveraged those permissions. Once installed, the malicious Chrome extensions did not need to exploit vulnerabilities in the operating system or bypass antivirus protections. They were already operating within a trusted context, which allowed them to observe, intercept, and manipulate data in real time.

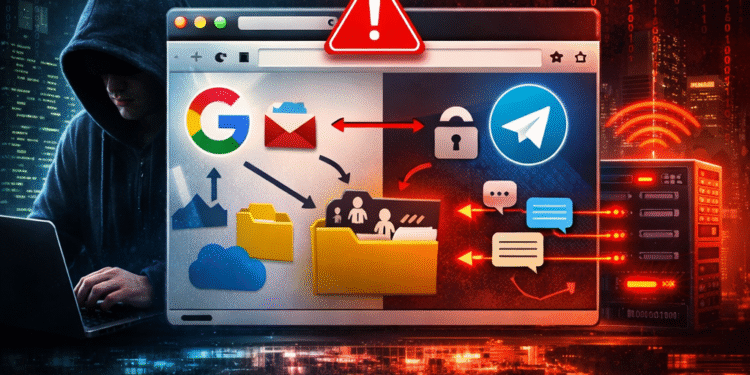
The Mechanics of Data Theft and Session Control
At the core of this campaign was a highly efficient data exfiltration pipeline. The extensions continuously monitored browser activity, collecting valuable information such as session tokens, authentication data, and user behavior patterns. This data was then transmitted back to attacker-controlled infrastructure, often at regular intervals, ensuring a steady stream of intelligence.
One of the most significant aspects of the attack was its focus on session hijacking rather than credential theft. In traditional attacks, hackers attempt to steal usernames and passwords. In this case, the goal was to capture active session tokens, which allow immediate access to accounts without needing login credentials.
This technique is especially effective against platforms like Google and Telegram, where persistent sessions are common. Once a session token is compromised, an attacker can effectively impersonate the user, accessing emails, files, and conversations as if they were the legitimate account holder. In some scenarios, sessions could even be replaced entirely, locking the user out while maintaining attacker access.
The implications are profound. It means that even strong passwords and multi-factor authentication can be bypassed if session integrity is compromised.
Invisible Manipulation: Code Injection at Scale
Beyond data theft, these extensions also demonstrated the ability to inject code into every webpage a user visited. This capability transforms the browser into an active attack platform rather than just a passive data source. By modifying web content in real time, attackers can introduce malicious scripts, alter page behavior, or present convincing phishing interfaces.
This kind of manipulation is nearly impossible for the average user to detect. A login page might look identical to the real thing, while quietly capturing credentials in the background. Payment forms could be altered to redirect funds. Even security warnings could be suppressed or modified to reduce suspicion.
The ability to inject code at scale across thousands of browsers creates a distributed attack surface that is both flexible and resilient. It allows attackers to adapt their tactics dynamically, deploying new payloads without requiring additional user interaction.
Persistence and Control: The Role of Backdoor Functionality
Another critical component of the campaign was persistence. Many of the extensions included hidden mechanisms that ensured continued access even after initial installation. These backdoors allowed the extensions to receive commands from remote servers, effectively turning each infected browser into a controllable node within a larger network.
This level of control opens the door to a wide range of follow-on attacks. Browsers can be instructed to open specific pages, execute scripts, or participate in coordinated campaigns such as ad fraud or traffic manipulation. The user, meanwhile, remains largely unaware that anything unusual is happening.
From an operational perspective, this transforms a simple extension into a long-term foothold. It is no longer just about stealing data once; it is about maintaining ongoing access and extracting value over time.
The Bigger Picture: Identity and the Modern Attack Surface
This campaign highlights a broader shift in cybersecurity strategy. Attackers are no longer focused solely on breaking into systems. Instead, they are targeting identity and session layers, where access can be gained without triggering traditional defenses.
In a cloud-first world, identity is everything. Access to a Google account can unlock email, storage, documents, and integrated services. A compromised messaging session can expose sensitive communications. By targeting these layers through the browser, attackers can achieve high-impact results with relatively low effort.
This is why browser security is rapidly becoming one of the most critical—and most overlooked—areas of defense. Organizations invest heavily in endpoint protection, network monitoring, and cloud security, yet often neglect the browser, where all these systems intersect.
Rebuilding Trust in the Extension Ecosystem
The presence of malicious Chrome extensions in the official store raises important questions about platform governance. While Google employs automated and manual review processes, this campaign demonstrates that determined attackers can still find ways to bypass controls.
Part of the challenge lies in the dynamic nature of extensions. An extension may appear benign during review but later introduce malicious functionality through updates. This delayed activation strategy makes detection significantly more difficult, as the initial version does not exhibit harmful behavior.
For users, this means that trust cannot be assumed based solely on availability in the store. Reputation, transparency, and necessity must all be considered before installing any extension. Even then, ongoing vigilance is required.
What This Means for Users and Organizations
For individual users, the takeaway is clear: the browser is no longer a safe default environment. It must be actively managed and secured. Extensions should be treated with the same level of scrutiny as any other software installation, if not more.
For organizations, the implications are even more significant. Managed devices, corporate accounts, and cloud platforms are all at risk if browser environments are not properly controlled. Policies around extension usage, permission management, and session security must become part of the broader cybersecurity strategy.
This is particularly relevant in remote and hybrid work environments, where employees rely heavily on browser-based tools. A single compromised extension can become an entry point into enterprise systems.
Final Thoughts: A Warning Sign for the Future
The discovery of these malicious Chrome extensions is not an isolated incident. It is a signal of where attacks are heading. As defenses improve at the network and endpoint level, attackers will continue to move closer to the user, targeting the interfaces where trust is highest and visibility is lowest.
The browser sits at the center of that intersection. It is where identity, data, and interaction converge. And as this campaign demonstrates, it is also where attackers can operate with remarkable effectiveness when given the opportunity.
The lesson here is not just about removing a few bad extensions. It is about recognizing that the security landscape has shifted. Protecting accounts and systems now requires protecting the environment in which they are accessed.
In that sense, the browser is no longer just a window to the internet. It has become one of the most critical frontlines in modern cybersecurity.
Related
-
AI Generated Code Security Risks
-
Why Rebooting Your Router Might Be the Simplest Cybersecurity Fix
-
Platform Engineering vs DevOps Explained