DevSecOps broken 2026 is becoming a serious concern as organizations struggle to keep security aligned with rapidly evolving development pipelines. What was once promoted as the answer to embedding security into DevOps workflows is now showing signs of strain. As software delivery accelerates and environments become more complex, security is often falling behind, creating gaps that attackers are actively exploiting.
The idea behind DevSecOps was simple: integrate security into every stage of the development lifecycle. In practice, however, many organizations have implemented fragmented tools, inconsistent processes, and automation that prioritizes speed over security. The result is a model that looks secure on the surface but is increasingly vulnerable underneath.
Why DevSecOps Broken 2026 Is Becoming a Reality
DevSecOps broken 2026 is not about failure in concept—it is about failure in execution. As pipelines have grown more sophisticated, they have also become harder to manage. Organizations are juggling multiple tools, environments, and integrations, often without a unified strategy. Security checks are added, but they are not always aligned, and in many cases, they are bypassed to avoid slowing down releases.
The pressure to deliver faster has created an environment where development speed is often prioritized over security integrity. Teams are rewarded for shipping code quickly, while security teams are expected to keep up without introducing friction. This imbalance is one of the core reasons why DevSecOps is breaking down in 2026.
As highlighted in the broader AI threat landscape 2026, attackers are evolving just as quickly as development pipelines, making these gaps even more dangerous.
The Complexity Problem in Modern Pipelines
Modern DevOps pipelines are no longer simple build-and-deploy systems. They are complex ecosystems involving containers, microservices, APIs, cloud infrastructure, and third-party integrations. Each component introduces its own set of security considerations, and managing them all effectively is a growing challenge.
DevSecOps broken 2026 is largely driven by this complexity. When pipelines span multiple platforms and services, visibility becomes limited. Security teams often lack a complete view of the environment, making it difficult to identify vulnerabilities before they are exploited.
This complexity is further amplified by the adoption of multi-cloud and hybrid cloud strategies. As organizations distribute workloads across different environments, maintaining consistent security policies becomes increasingly difficult. The more moving parts there are, the more opportunities exist for misconfigurations and oversight.
Security Tools Are Not Keeping Up
One of the biggest issues contributing to DevSecOps broken 2026 is the disconnect between security tools and modern development workflows. Many security solutions were designed for static environments, not dynamic, cloud-native pipelines that change constantly.
As a result, security tools are often reactive rather than proactive. They detect issues after code has already been deployed, rather than preventing them during development. This lag creates a window of opportunity for attackers, who can exploit vulnerabilities before they are identified and fixed.
In addition, the sheer number of tools being used can create its own problems. Organizations may have separate tools for code scanning, container security, infrastructure monitoring, and compliance checks. Without proper integration, these tools generate fragmented insights that are difficult to act on.
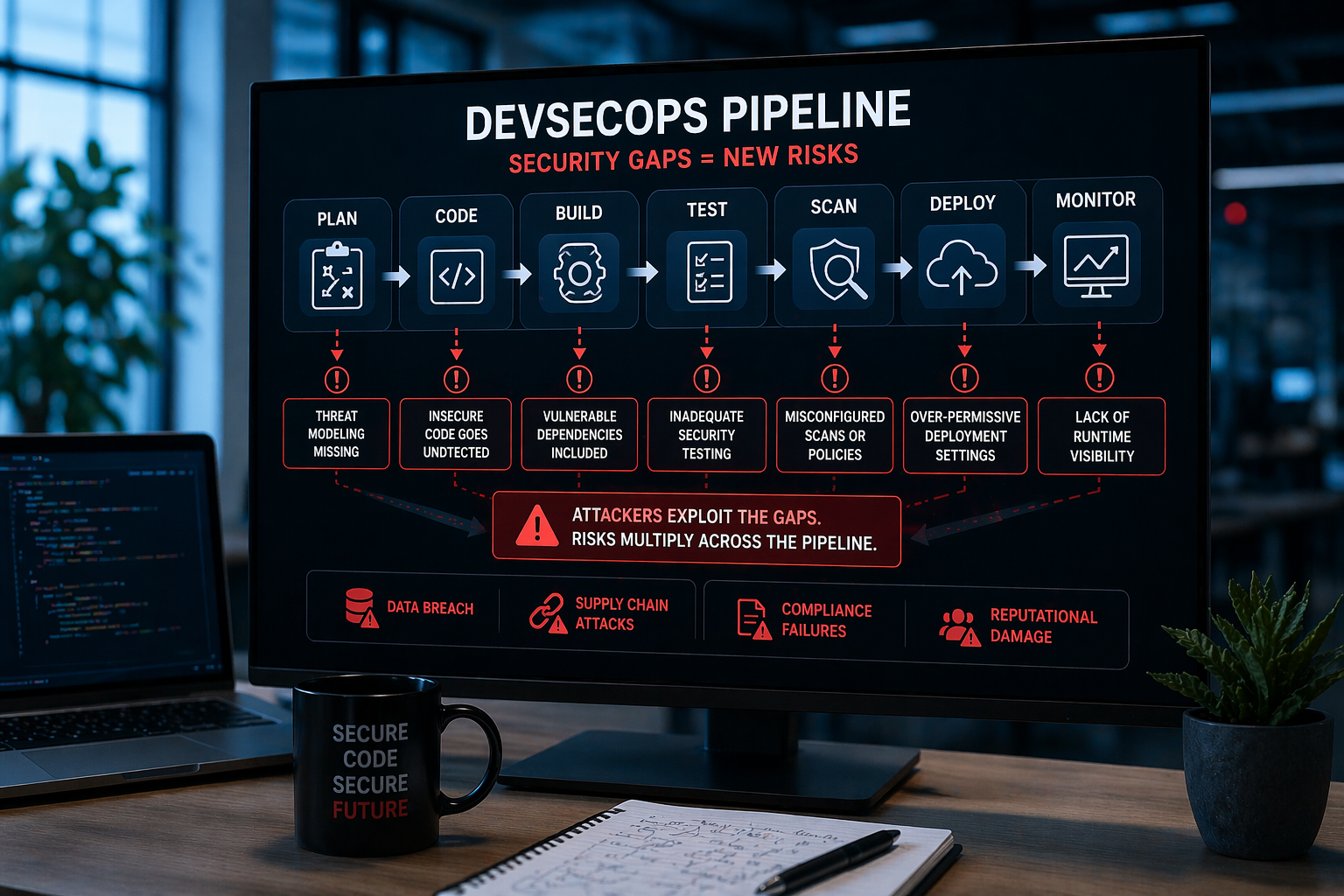
The Rise of Pipeline-Based Attacks
Attackers are increasingly targeting the pipeline itself. Instead of attacking applications directly, they are focusing on the systems that build and deploy those applications. This shift is a direct response to the weaknesses exposed by DevSecOps broken 2026.
Pipeline-based attacks can take many forms, including injecting malicious code during the build process, exploiting misconfigured CI/CD systems, or compromising credentials used in automation scripts. Once inside the pipeline, attackers can distribute malicious code at scale, affecting multiple applications simultaneously.
As discussed in our analysis of AI-generated code security risks the growing reliance on automation and AI-driven development is creating new entry points for attackers. These systems can introduce vulnerabilities faster than they can be detected, especially when security checks are not properly integrated.
Why Automation Alone Isn’t Enough
Automation is a core component of DevSecOps, but it is not a complete solution. DevSecOps broken 2026 highlights the limitations of relying too heavily on automated security checks without proper oversight. While automation can improve efficiency, it cannot replace human judgment.
Automated tools are only as effective as the rules and data they are based on. They may miss subtle vulnerabilities, misclassify risks, or generate false positives that teams begin to ignore over time. This creates a dangerous cycle where real threats can slip through unnoticed.
Organizations that rely solely on automation are often lulled into a false sense of security. They assume that because checks are in place, their systems are protected. In reality, these checks may not be comprehensive or up to date with the latest threat landscape.
How Organizations Must Fix DevSecOps
Fixing DevSecOps broken 2026 requires a shift in both mindset and strategy. Organizations need to move away from fragmented, tool-driven approaches and adopt a more integrated model where security is embedded into every aspect of the pipeline.
This starts with improving visibility. Teams must have a clear understanding of their entire pipeline, including all dependencies and integrations. Without this visibility, it is impossible to manage risk effectively.
Collaboration is also critical. Security, development, and operations teams need to work together as a unified unit, rather than operating in silos. This ensures that security considerations are built into the development process from the start, rather than added as an afterthought.
Finally, organizations must balance automation with human oversight. Automated tools should support security efforts, not replace them. By combining the speed of automation with the insight of experienced professionals, companies can build more resilient pipelines that are capable of withstanding modern threats.
The Bottom Line
DevSecOps broken 2026 is not a sign that the concept has failed—it is a sign that it has not been fully realized. The challenges organizations are facing today are the result of rapid growth, increasing complexity, and a failure to adapt security practices to match the pace of innovation.
As pipelines continue to evolve, so too must the strategies used to secure them. Organizations that recognize this shift and take proactive steps to address it will be better positioned to manage risk and protect their systems. Those that do not will continue to face growing vulnerabilities in an increasingly hostile threat environment.
DevSecOps broken 2026 continues to expose critical gaps in modern pipelines as organizations struggle to balance speed and security.