For years, software security was treated as a final checkpoint before release. Security teams would perform vulnerability scans or penetration tests once development was largely complete, often discovering issues at the worst possible time—right before deployment.
Today that model is rapidly disappearing.
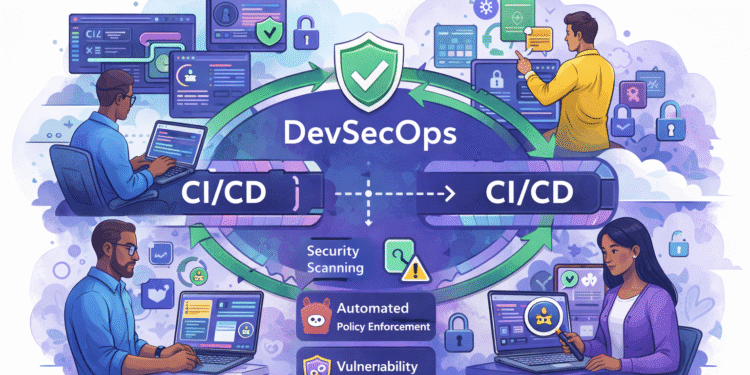
Modern software delivery environments are increasingly adopting DevSecOps pipelines, where security testing, policy enforcement, and vulnerability detection occur continuously throughout the development lifecycle. Instead of acting as a final gate, security is becoming a built-in component of CI/CD pipelines.
This shift is fundamentally changing how organizations protect applications while maintaining the speed and agility demanded by modern development teams.
Why Traditional Security Models Failed
Traditional application security workflows were designed for a much slower development cycle. Software updates were released periodically, often on quarterly or annual schedules. Security testing could be performed manually without significantly slowing the release process.
Modern development environments operate very differently.
Organizations now deploy software multiple times per day using automated pipelines. Applications are composed of microservices, containers, APIs, and third-party dependencies. Cloud-native architectures introduce thousands of dynamic infrastructure components that change constantly.
Under these conditions, traditional security practices simply cannot keep up.
When security reviews occur too late in the development process, teams often face two bad options:
• delay the release while issues are fixed
• ship software with known vulnerabilities
Neither option is acceptable in high-velocity DevOps environments.
What DevSecOps Pipelines Change
DevSecOps integrates security controls directly into CI/CD pipelines so vulnerabilities are detected and addressed earlier in the development lifecycle.
Instead of waiting until deployment, security tools run automatically during multiple stages of the pipeline.
These stages typically include:
• source code scanning
• dependency analysis
• container image scanning
• infrastructure configuration validation
• runtime security monitoring
By embedding security into pipelines, organizations create continuous security feedback loops that help developers address issues immediately after code changes are introduced.
This dramatically reduces the time required to detect and remediate vulnerabilities.
Security Testing Moves Left
One of the most important principles behind DevSecOps is shift-left security.
Shift-left means moving security testing earlier in the development lifecycle—closer to the point where code is written.
Instead of discovering vulnerabilities weeks later during manual testing, developers receive immediate feedback during code commits and build processes.
Modern DevSecOps pipelines often include tools such as:
• Static Application Security Testing (SAST)
• Software Composition Analysis (SCA)
• Secret detection
• dependency vulnerability scanning
These tools automatically analyze code and dependencies to identify potential vulnerabilities before they progress further through the pipeline.
Developers can then fix problems quickly while the context of the change is still fresh.
The Rise of Automated Security Policies
Another major shift in DevSecOps pipelines is the use of automated policy enforcement.
Security teams increasingly define policies that pipelines enforce automatically. These policies may include rules such as:
• blocking builds that include known vulnerable libraries
• rejecting container images with critical vulnerabilities
• preventing infrastructure misconfigurations in cloud deployments
Instead of relying on manual reviews, these policies become part of the pipeline itself.
This approach ensures consistent enforcement across development teams while reducing the burden on security professionals.
Container and Cloud Security Integration
Modern applications frequently run in containerized environments managed by orchestration platforms such as Kubernetes.
DevSecOps pipelines now incorporate specialized security tools designed to analyze container images and infrastructure configurations.
These tools identify issues such as:
• outdated base images
• insecure container configurations
• exposed secrets
• vulnerable dependencies
Infrastructure-as-code templates are also scanned automatically to ensure that cloud environments comply with security best practices before deployment.
This proactive approach helps prevent security misconfigurations that could expose sensitive systems.
The Role of Runtime Security
While DevSecOps pipelines focus heavily on pre-deployment testing, security does not stop once software reaches production.
Runtime security tools monitor applications and infrastructure to detect suspicious behavior or attacks in real time.
Examples include:
• abnormal network activity
• privilege escalation attempts
• unexpected container processes
• suspicious API usage
When integrated with CI/CD pipelines, runtime security insights can feed back into development workflows, helping teams identify vulnerabilities that were missed during earlier stages.
Security Vendors Driving the DevSecOps Movement
The rapid growth of DevSecOps pipelines has fueled an entire ecosystem of security platforms designed specifically for modern development environments.
Companies such as Snyk, Wiz, Aqua Security, and Sysdig have built solutions that integrate directly with CI/CD pipelines and cloud-native infrastructure.
These platforms provide automated scanning, vulnerability analysis, and policy enforcement capabilities that allow organizations to maintain security without slowing development velocity.
Major DevOps platforms—including GitHub, GitLab, and AWS—are also expanding their built-in security capabilities to support DevSecOps workflows.
Developer Experience Matters
One challenge DevSecOps teams face is ensuring that security tools do not create friction for developers.
If security processes slow pipelines or produce overwhelming numbers of alerts, developers may attempt to bypass them.
Successful DevSecOps implementations focus on developer-friendly security tools that provide clear guidance and actionable insights.
The goal is not simply to identify vulnerabilities but to help developers fix them quickly and efficiently.
By improving developer experience, organizations can ensure that security becomes a natural part of the development workflow rather than an obstacle.
The Future of DevSecOps Pipelines
As software ecosystems continue to grow in complexity, DevSecOps pipelines will become even more critical.
Future DevSecOps platforms are likely to incorporate advanced technologies such as:
• AI-driven vulnerability detection
• automated remediation suggestions
• predictive security risk analysis
• real-time policy enforcement across distributed environments
These capabilities will help organizations secure increasingly complex systems without sacrificing the speed of modern software delivery.
Conclusion
The rise of DevSecOps pipelines marks a major shift in how organizations approach application security.
Instead of treating security as a final checkpoint before deployment, modern development teams are embedding security directly into CI/CD workflows.
This approach enables faster vulnerability detection, stronger policy enforcement, and improved collaboration between development, operations, and security teams.
As software delivery continues to accelerate, organizations that adopt DevSecOps pipelines will be better positioned to maintain both speed and security in an increasingly complex digital landscape.